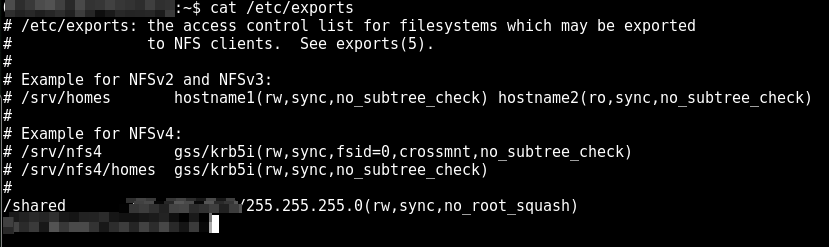
Recently during a penetration testing assessment I was able to get Linux Privilege Escalation using weak NFS permissions in “/etc/exports”. Initially I got […]
You may also like
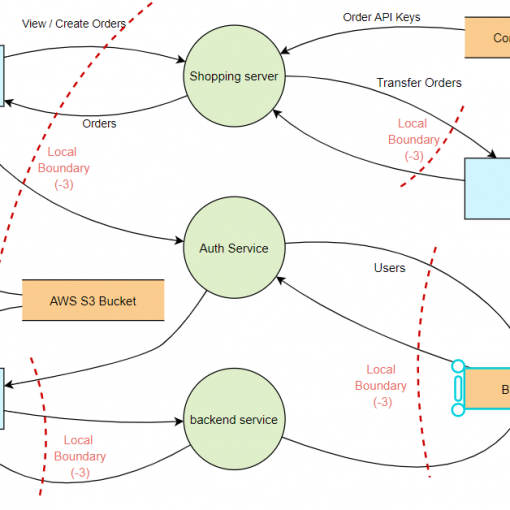
STRIDE Threat modelling Which THREAT modelling framework/methodology should I go for? This is a very common question nowadays, since the “Shift-left revolution”, […]
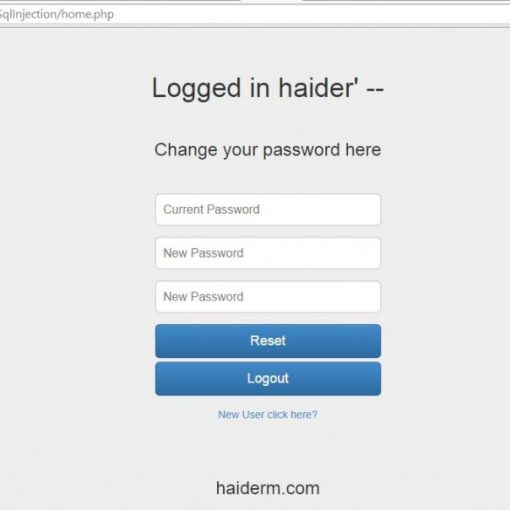
Introduction Second Order SQL injection is an application security vulnerability, it occurs when user-submitted values are stored in the database, and then […]
Introduction During Penetration testing engagement you are required backdooring PE file with your own shellcode without increasing the size of the executable […]