
The Perfect System for Advanced Access Control




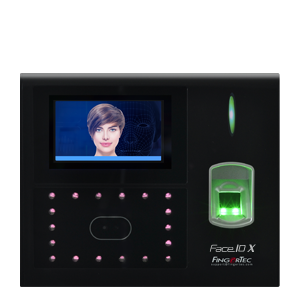
| Prevent budding punching and anti-spoofing with Fingerprint/Facial Recognition | |
| High reliability and low false acceptance rate | |
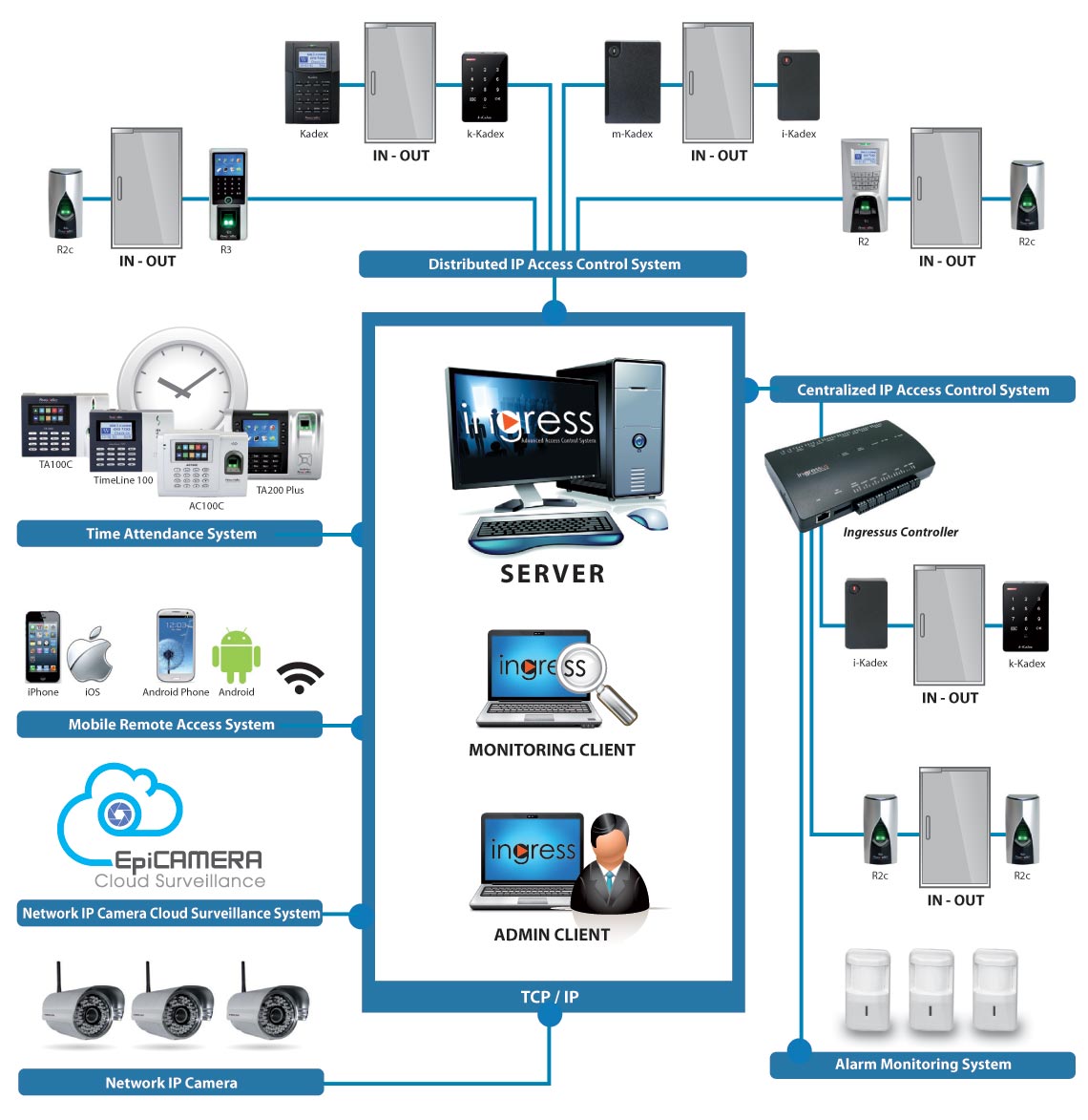
| Connect up to 99 FingerTec devices at the same time | |
| Multiple data transfer channels: TCP/IP, Dynamic DNS, RS232/485, 3G or USB Flash Disk |
| Immediate synchronisation of data to the device after changes are made in Ingress | |
| Time synchronisation date and time of all terminals automatically or manually | |
| Sets a specific time to download data from FingerTec Time Attendance terminals automatically | |
| Set a specific time to back up the database of the software |


| Quick setup wizard to facilitate simple configuration during initial start- up | |
| Allows easy addition of large quantities of users by Batch Create Users feature | |
| Provides configuration templates to reduce the time required to configure the system | |
| Different user interface themes are available and simple to understand organisation with a “tree structure” design |
| Supports 10 levels of departments | |
| Track users' card management records and history | |
| Detailed permissions and user rights for the access, display and control of subsystems | |
| Integration with OFIS-Z for fingerprint registration station |


| Up to 9 intuitive graphical maps are completely customisable for real-time monitoring | |
| Remote control access and alarm activities directly from the monitoring station | |
| Multiple workstation monitoring capabilities | |
| Real-time alarm or event logs to ensure all events are completely documented for the entire system |
| Interlocking | |
| Anti-passback | |
| Multi-card operation | |
| Fire alarm linkage | |
| Multiple verification setting | |
| Door-always-open schedule |


| Organise alarm alerts and set alarm priorities to optimise response time | |
| Configure event priorities from a total of 62 event types | |
| Offline door events, alarm events & terminal connection events | |
| Automatically sends email and notifications to defined recipients when an event is detected in the system | |
| Customisable sound alerts for every priority | |
| Push notifications are available for iOS and Android device users |
| Provides up to 3-time zone settings per day | |
| Allows time-based access permission to be defined per weekday | |
| Provides holiday configuration & holiday time zone settings |

| Weekly schedules available with 3 pairs of IN/OUT columns for attendance monitoring | |
| Supports group or personal duty roster setup | |
| Supports leave and holiday management | |
| Generate attendance sheets, and instantly add, edit or delete attendance records | |
| Terminal data audit list enables raw data checking and export | |
| Timer feature for automatic download of data after a specified interval | |
| Support up to 9 digits of work codes | |
| Integrated with 20+ payroll. |
| Integrated with Milestone's Xprotect series and EpiCamera's cloud storage solutions | |
| Users can quickly track, or playback captured video clips or pictures of the door event | |
| Supports live feed directly from the IP Camera | |
| The Play Video Window supports frame selection, variable speed, pause and export to AVI and JPG files |


| Screen-lock function; automatic logout after the timeout period | |
| Supports customised digital watermark imprint for document uniqueness | |
| Provides detailed history records and audit trail functions for tracking past configuration changes | |
| Optional fingerprint login for system administrators |
| 33 Pre-configured reports | |
| Comprehensive event filtering | |
| Support exporting reports in up to 10 formats: xls, txt, PDF, csv, etc. |












I should also check if there's any official statement from Trisha or her team regarding this. If there isn't, the safest approach is to mention the lack of credible information and advise against engaging with unverified content. Additionally, highlight the importance of respecting privacy and avoiding sharing content that's altered or sensitive.
Also, considering the user's intent—maybe they're looking for a fictional write-up, but the request is for a factual one. The user might have stumbled upon some altered media and is curious about the backstory. But I must ensure that responding to this doesn't contribute to the circulation of potentially false or private material.
I should check if there's any real incident related to this. Maybe it's about a photo or video that was leaked or altered. The word "patched" might refer to the content being doctored or fixed in some way. Sometimes, in the entertainment industry, privacy breaches occur where images or videos are leaked, leading to the subject trying to cover themselves (hence "patched"). Alternatively, "patched" could mean the content was modified to cover up sensitive areas.
However, as an AI, I need to be cautious. Spreading unverified information, especially if it's false or maliciously altered, can be harmful. Trisha Krishnan is a public figure, and her right to privacy is important. I should look up credible sources to see if there's any legitimate context. If there's no verified information, I shouldn't assume or fabricate details.
In summary, the response should clarify that there's no reliable information on this topic, caution against spreading unverified material, and emphasize respecting privacy. It should also steer the user towards factual information about Trisha Krishnan's career if that's their real interest.